Australia has had it rough in recent weeks with Australia Cyber Attacks on the rise.
Australia has already seen 3 major companies attacked in the last few weeks.
Optus saw around 10 million Customers affected, taking the usual data such as names, emails, phone numbers, but also had critical data like Drivers License, Passport Numbers and Medicare Numbers.
Medibank Private found suspicious activity on their Network, but so far the investigation has shown no sensitive data accessed.
Woolworths MyDeals was hit by an attack that affected 2.2 million customers, taking the usual, names, emails, numbers, addresses and even Date of Birth. 1.2 million is said to only have had their emails only taken.
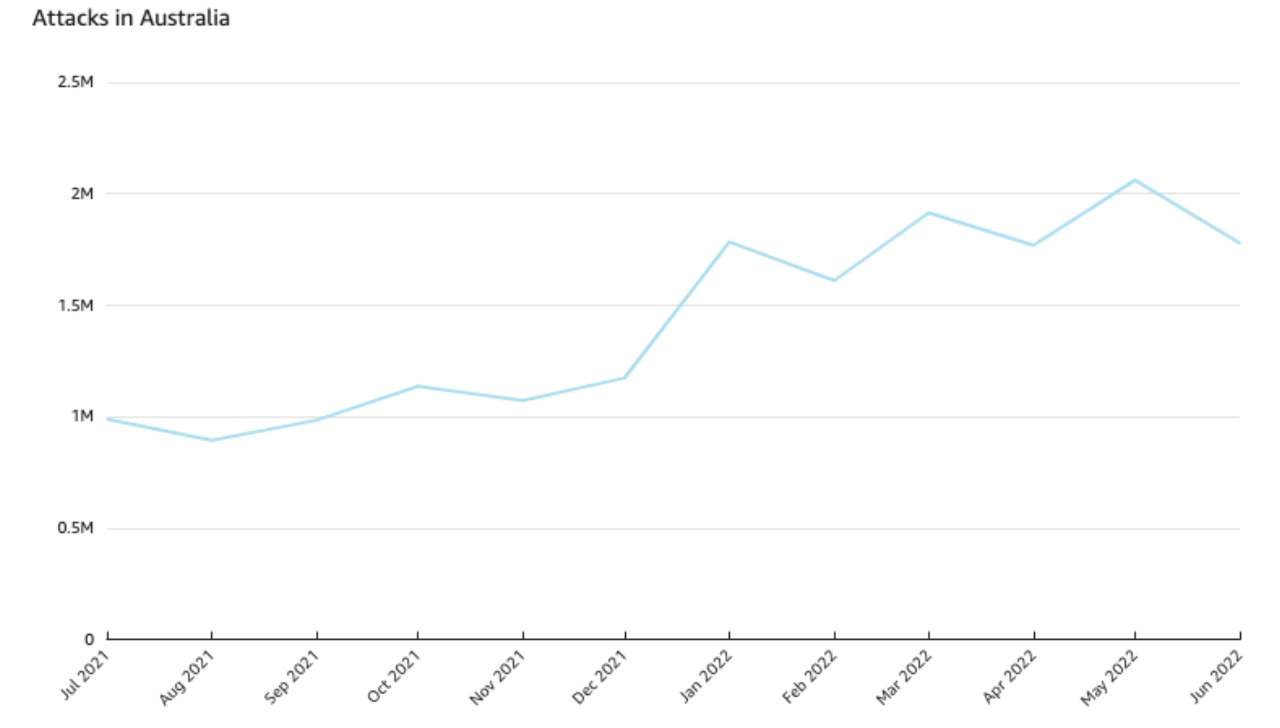
Imperva Research has seen an increase of 81% in Cyber attacks between July 2021 to June 2022 with attacks classed as “Critical” has increased by 230% between August 2021 and May 2022.
Financial, retail, and business services had the most attacks in one year…
Financial, Retail, and Business Services were among the most hit with attacks in one year, with financial and retail sites also having the largest jump in attacks.
“Incidents targeting financial sites, specifically, rose almost 200% in 2022. Financial cybercrime is a lucrative industry, and attackers are after credit cards, account information, banking details, and crypto wallets, among other things. Business Services may be targeted for a variety of reasons, including scraping data for competition, stealing customer databases or other information, or because small businesses may not have the same security controls on their sites as larger companies.” the report says.
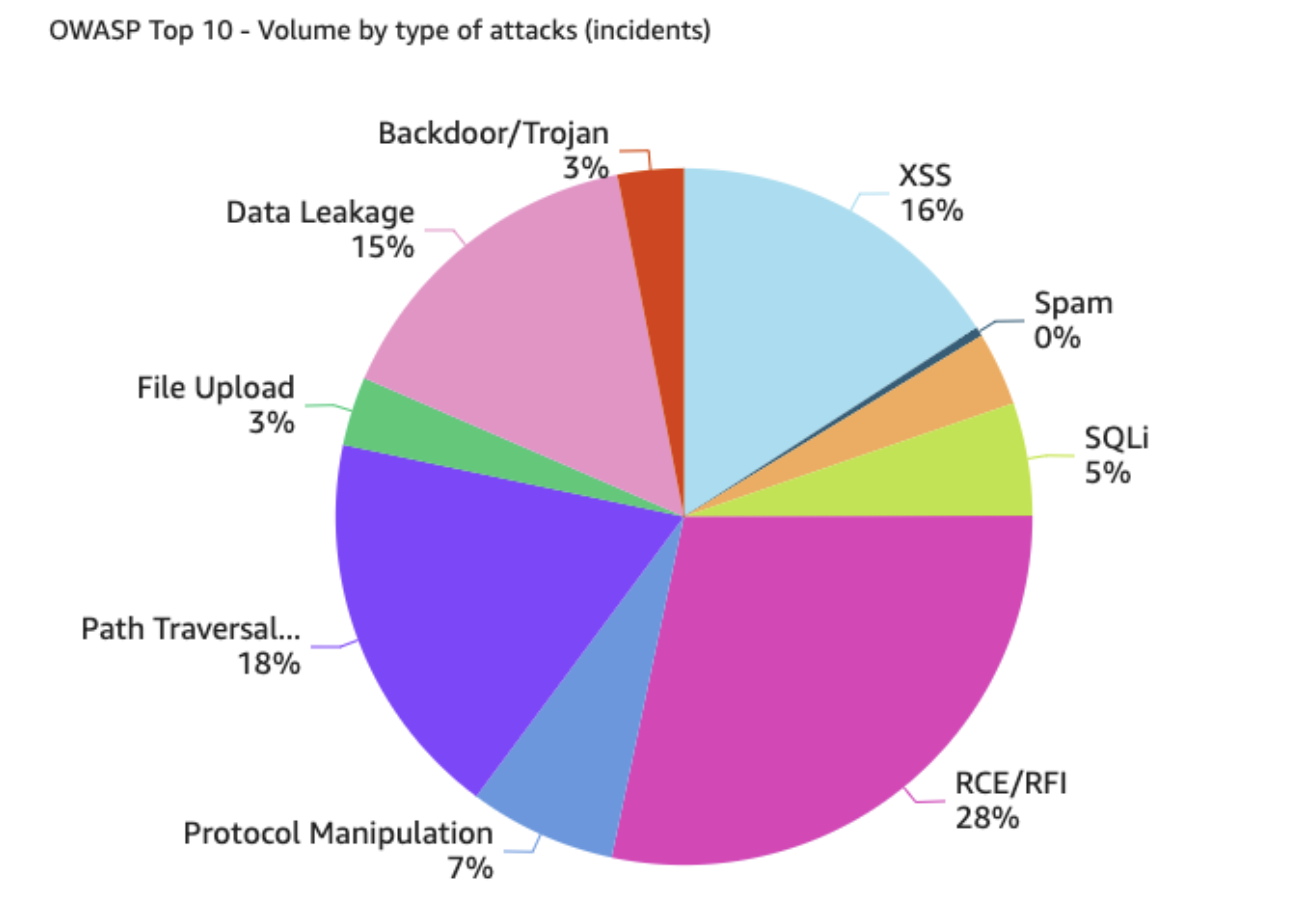
The Top 3 attack vectors include:
- Remote Code Execution (RCE)
- Path Traversal and Local File Inclusion (LFI)
- Cross-site Scripting (XSS)
RCE allows attackers to execute malicious code on a targeted device, which can be used to get information out of a system. RCE can be modified to fit any target, and can be combined with social engineering attacks and malware to gain easier access to systems.
LFI is used to trick a web application into exposing files on a server.
XSS occurs when an attacker injects malicious code into a normal website.
So, why Australia?
According to the Credit Suisse Research Institute’s (CSRI) Global Wealth Report 2022, Australia is the wealthiest country in the world when it comes to wealth per adult ($273,900 USD). Cybercriminals would see Australia and its citizens as fruitful targets for identity theft, financial fraud, and other financially motivated scams.
Considering that SCAMWATCH and other organizations had a combined report of a record $2+ billion loss in 2021, leveraged by the Pandemic and Businesses not prepared to transition into the Digital sector, commonly rushing into it, just goes to show that Australia isn’t quite up to par on managing security both personally and in business.
What can you do?
For Personal, you need to ensure you have security on your devices and keep things up to date.
We recommend Norton 360 by Symantec for your Windows PC, Apple Mac, Android and iOS devices.
Keep your devices security, apps and system up to date.
Use strong passwords for each service, making sure they are different each time.
Passwords should at least have 8 characters minimum in length, but the longer, the better – they should have at least 1 Number, 1 Uppercase, 1 Lowercase and 1 Symbol, but again, the more, the better.
To alleviate the pain of remembering passwords, you can use a password manager like Norton Password Manager (which is Free and available as an app on your Phone and Tablet Devices or as an extension on Web Browsers on your Computer Devices). The Password Manager means you need to remember 1-2 Passwords only, related to the Service (Password for the Account and maybe Password for the Manager itself – Norton Password Manager has a Norton Account Username and Password and Vault Password to remember).
Remember, losing access to your Password Manager will mean you lose every password saved, so make sure you have a physical copy of mission critical usernames and passwords handy as a safety net to use for recovery, making sure it is in a safe place, like a Fireproof Safe.
Ensure you utilize Recovery options that are easy for you, hard for hackers and scammers. If it asks for secret questions, make sure you use them with hard information nobody can get, other than those who you trust.
If the service has Recovery Codes, keep them with your Hard Copy List.
One of the best complimentary security services you can use is Multifactor Authentication (MFA).
Enable this where possible. Different types include Calls, Text Message, Email and Apps.
Apps like Google Authenticator and Microsoft Authenticator is available to use to get One-Time Codes and/or “Approvals”.
Text Messages to your registered Mobile is a good backup if you cannot use your App for some reason.
Email is your 3rd resort if you lost your mobile device and cannot access the App or Text Message. (Note: Email being compromised means your Accounts can be compromised when the code can be sent to your email. So it is important that your Email Account is super strong and all measures of security and warnings if you do get compromised, is ready for you to mitigate.
Where all else fails, some services provide recovery codes where you cannot access ANY of the above methods.
For Business, following best practises of Personal above is good, however, you need to highly consider ensuring you have the best possible security measures implemented as much as possible.
You may have extra devices and services/assets to consider when it comes to Security.
You should audit all your assets and ensure you have the best possible security. This includes Computer Device Security, Email Security, Website Security, Customer Information Security.
You should create a Security Policy for your business. A policy helps everyone know what/where/when and how to handle Security and if an incident occurs.
If you have any questions or concerns about your Personal or Business Security, contact us ASAP so we can help rectify any shortcomings.